Trezor.io/start: Your Ultimate Guide to Securing Crypto
Step-by-step setup, security tips, and best practices for beginners and mid-level crypto users
What is Trezor and Why Trezor.io/start Matters
Trezor is a leading hardware wallet designed to keep your cryptocurrency assets safe from hacks, malware, and phishing attacks. Unlike software wallets that rely on internet connectivity, Trezor stores your private keys offline, providing the ultimate layer of security. The Trezor.io/start portal is the official setup gateway where you can initialize your device, create a secure PIN, and back up your recovery seed. Whether you’re a crypto newbie or someone familiar with exchanges and wallets, this portal simplifies the onboarding process.
Quick Highlight:
Trezor.io/start ensures that every device setup is authentic and secure, eliminating risks of counterfeit hardware or phishing websites. Always access Trezor setup directly through this URL for maximum security.
Step-by-Step Guide to Setting Up Your Trezor Wallet
- Unbox and Connect: Carefully remove your Trezor device from packaging. Connect it via USB or USB-C to your computer.
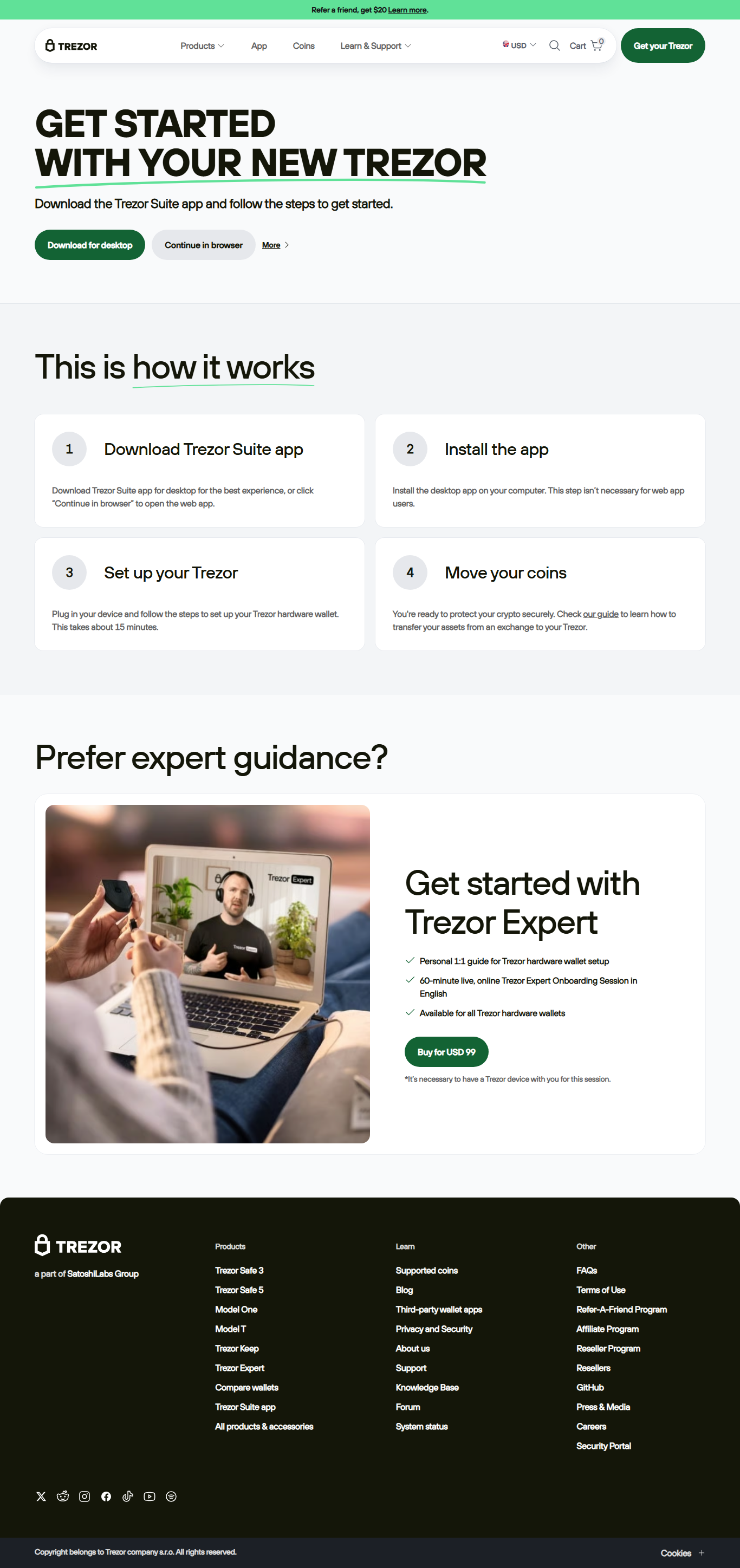
- Access Trezor.io/start: Open your browser and navigate to https://trezor.io/start. The website will guide you through downloading the Trezor Suite.
- Install Trezor Suite: Download and install the official app. Trezor Suite allows you to manage multiple cryptocurrencies, check balances, and receive/send funds securely.
- Firmware Update: If prompted, update your Trezor’s firmware. Always confirm updates directly on the device screen to avoid malicious attacks.
- Create PIN and Recovery Seed: Set a strong PIN and write down your 24-word recovery seed. Store it in a secure, offline location. This seed is your ultimate backup.
- Verify Wallet: Follow the Trezor Suite prompts to verify your wallet and confirm the recovery seed.
Pro Tip:
Never take a screenshot of your recovery seed or store it digitally. Treat it like gold — a lost seed means lost crypto forever.
Understanding the Security Features of Trezor
Trezor is more than just a USB device. Its security ecosystem combines hardware-level encryption, offline private key storage, and advanced passphrase protection. Here’s how some of its key security features work:
- PIN Protection: Each login requires a unique PIN that’s never transmitted online.
- Passphrase Entry: Optional feature adding a hidden wallet layer, protecting funds even if the recovery seed is exposed.
- Firmware Verification: Prevents malicious code by confirming updates directly on the device screen.
- Recovery Seed Backup: 24-word seed ensures wallet recovery even if the device is lost or damaged.
Comparison: Hardware vs Software Wallets
| Feature | Hardware Wallet (Trezor) | Software Wallet |
|---|---|---|
| Security | Offline, encrypted keys | Online, vulnerable to malware |
| Backup | 24-word recovery seed | Depends on cloud or device storage |
| Ease of Use | Simple guided setup via Trezor.io/start | Varies by app; often more intuitive |
| Cost | Paid device ($60–$200) | Mostly free |
Advanced Tips for Intermediate Users
Once you are comfortable with the basics, Trezor offers advanced features that crypto enthusiasts can leverage:
- Multi-Currency Management: Trezor supports over 1,800 coins, including Bitcoin, Ethereum, and ERC-20 tokens.
- Passphrase Hidden Wallets: Create multiple wallets from the same device using unique passphrases for privacy.
- Third-Party Integration: Connect Trezor to DeFi apps and exchanges like Uniswap or Kraken for seamless trading while keeping keys offline.
- Security Audits: Regular firmware updates ensure your wallet stays protected against emerging threats.
Did You Know?
Trezor wallets were among the first hardware wallets ever created (2014) and remain open-source, allowing the crypto community to verify their security protocols. This transparency is why many investors trust Trezor for long-term storage.
FAQs About Trezor.io/start
A: Yes! The portal is mobile-friendly, but for optimal security, use a trusted desktop browser during initial setup.
A: You can restore your wallet on any Trezor device using your 24-word recovery seed.
A: Trezor supports a wide range, including Bitcoin, Ethereum, Litecoin, ERC-20 tokens, and many more. Always check the official list in Trezor Suite for updates.
Final Thoughts
Trezor.io/start is your trusted gateway to cryptocurrency security. From beginners taking their first steps to mid-level users managing diverse crypto portfolios, following the official setup process guarantees a safe and seamless experience. Remember: your recovery seed is sacred, your firmware updates are crucial, and your hardware wallet is the key to true crypto ownership.